Information security management system
Formalize and automate the management of business and IT services to increase delivery quality and minimize delivery costs
In a nutshell Request demo Free trial
Service detection & documentation
Service detection & documentation
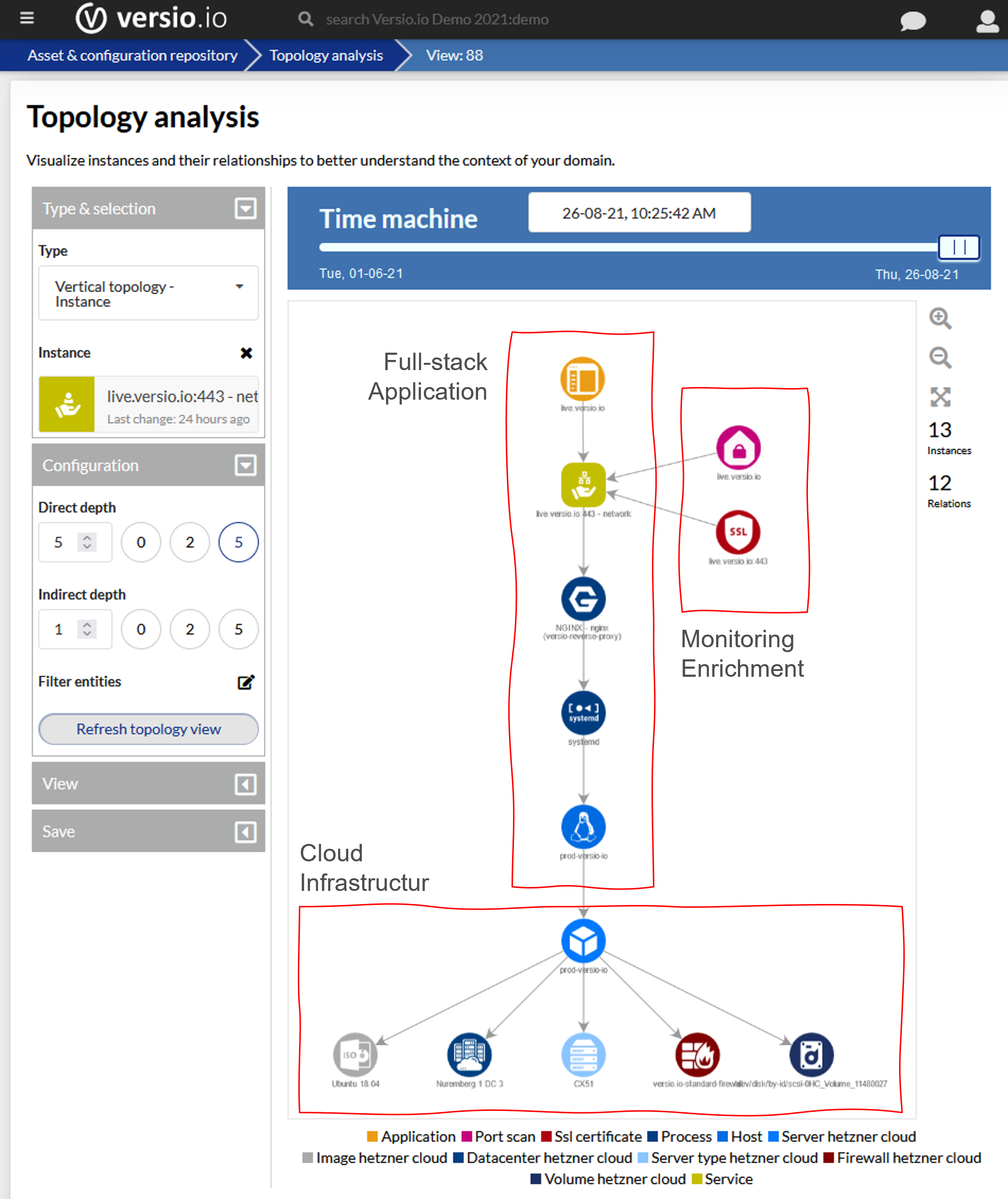
Service discovery and continuous documentation of service configuration is the critical foundation for executing service management.
Versio.io offers you a full-stack service discovery auto-mechanism. The service topology can be extended with service components from other data sources (cloud provider, IT service management) to achieve a complete picture of the service.
All components as well as the topology are historized. This means that you can view the state of the service at any desired point in time.
The term 'service' is often understood differently by different people. Attached are a few examples of what we consider a service to be:
- Application (e.g. CRM application)
- Application programming interface (API, e.g.)
- Batch-job (e.g. billing, backup)
- Infrastucture components (e.g. host, virtual machine)
- Network
- Business service (e.g. first level support)
Service change monitoring
Service change monitoring
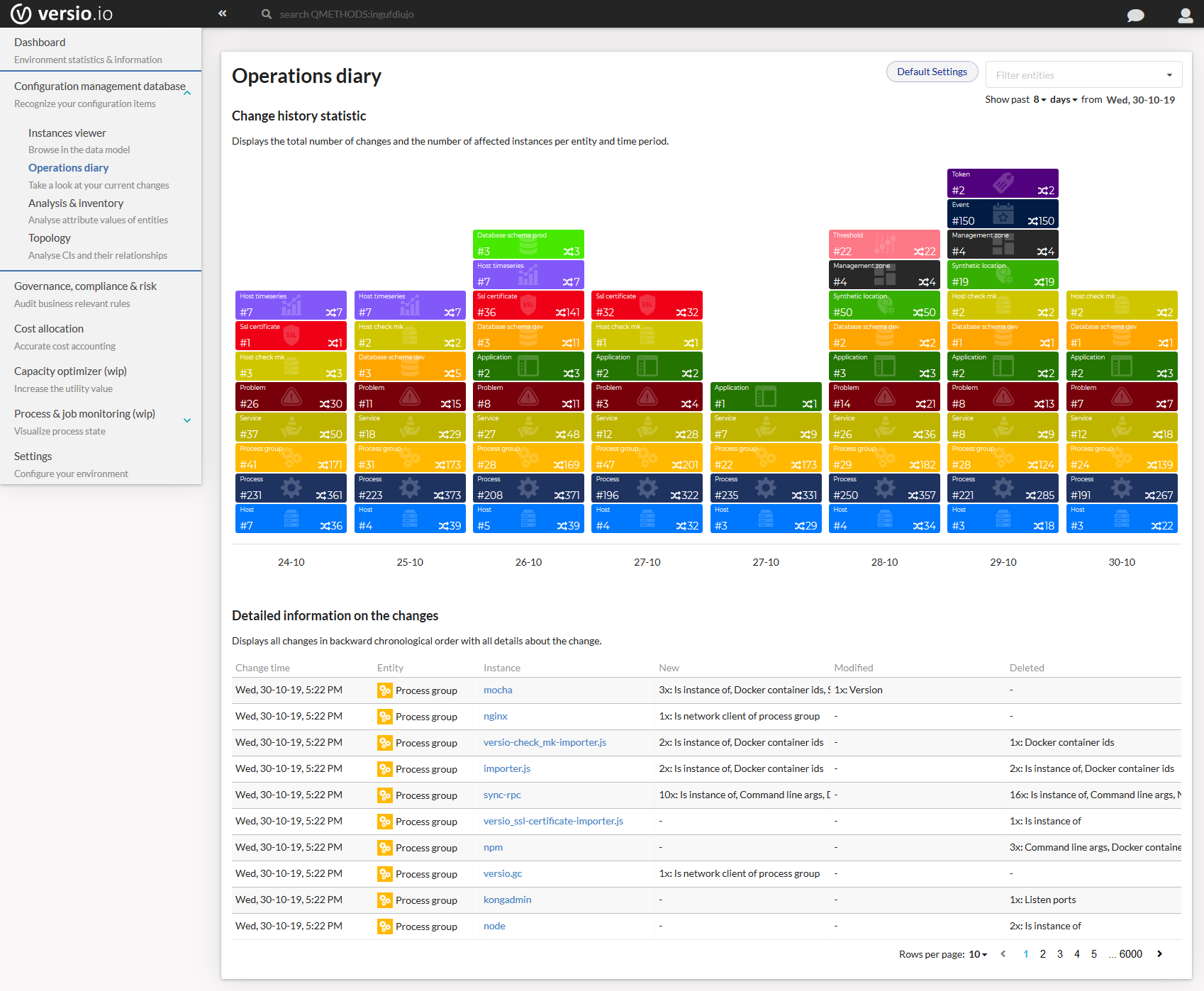
To manage a service it is necessary to perceive its changes in order to be able to react to them.
Versio.io continuously captures the state of each component of a service and can thus detect the change. In the Versio.io Operation Diary all changes are filtered and displayed transparently for all service components.
Service governance & compliance

Service governance & compliance
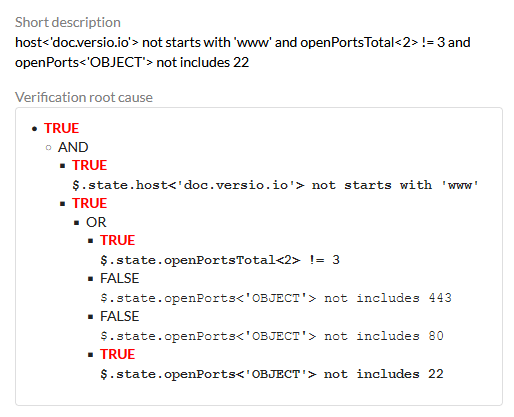
The change of a component of a service can affect its delivery quality or its cost.
Versio.io offers the possibility to verify any change according to customer-specific functional, operational or security-relevant requirements. It can detect and document the occurrence as well as the resolution of a violation. On the basis of corresponding events, customer-specific alerts can be executed.
Practical examples of how to verify a service change:
- Operational requirements (naming conventions, anti-pattern configuration etc.)
- Identify known IT vulnerabilities
- Detect outdated product versions of service components
- Detect product versions no longer maintained or serviced by the manufacturer
Service root cause analysis
Service root cause analysis
When the service provided is compromised, you want to quickly identify the root cause of the problem.
Versio.io offers two options to identify the root cause. The first one is the Operation Diary, which shows you the change in the period of the problem. A change can be the trigger of the problem.
Furthermore, Versio.io can verify the content of each change and thus identify and alert an unwanted condition in business real-time.
Service level agreements & objectives
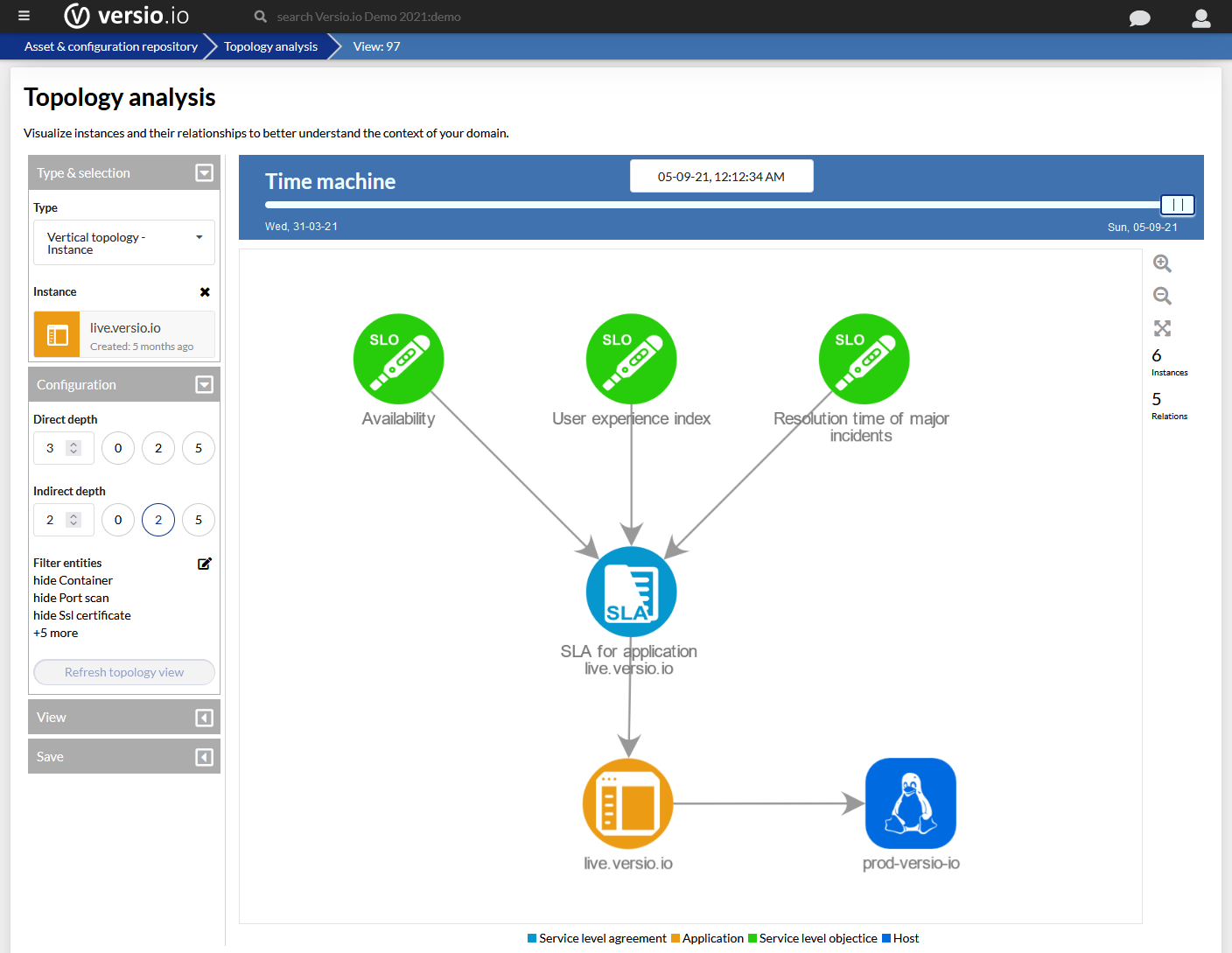
Service level agreements & objectives
Identified violations are documented in the form of verification results and events in an audit-proof manner.
Violation result and related events can trigger further actions like e-mail or chat notification, execution of IT operations cookbooks, creation of monitoring events, etc.
Service cost allocation
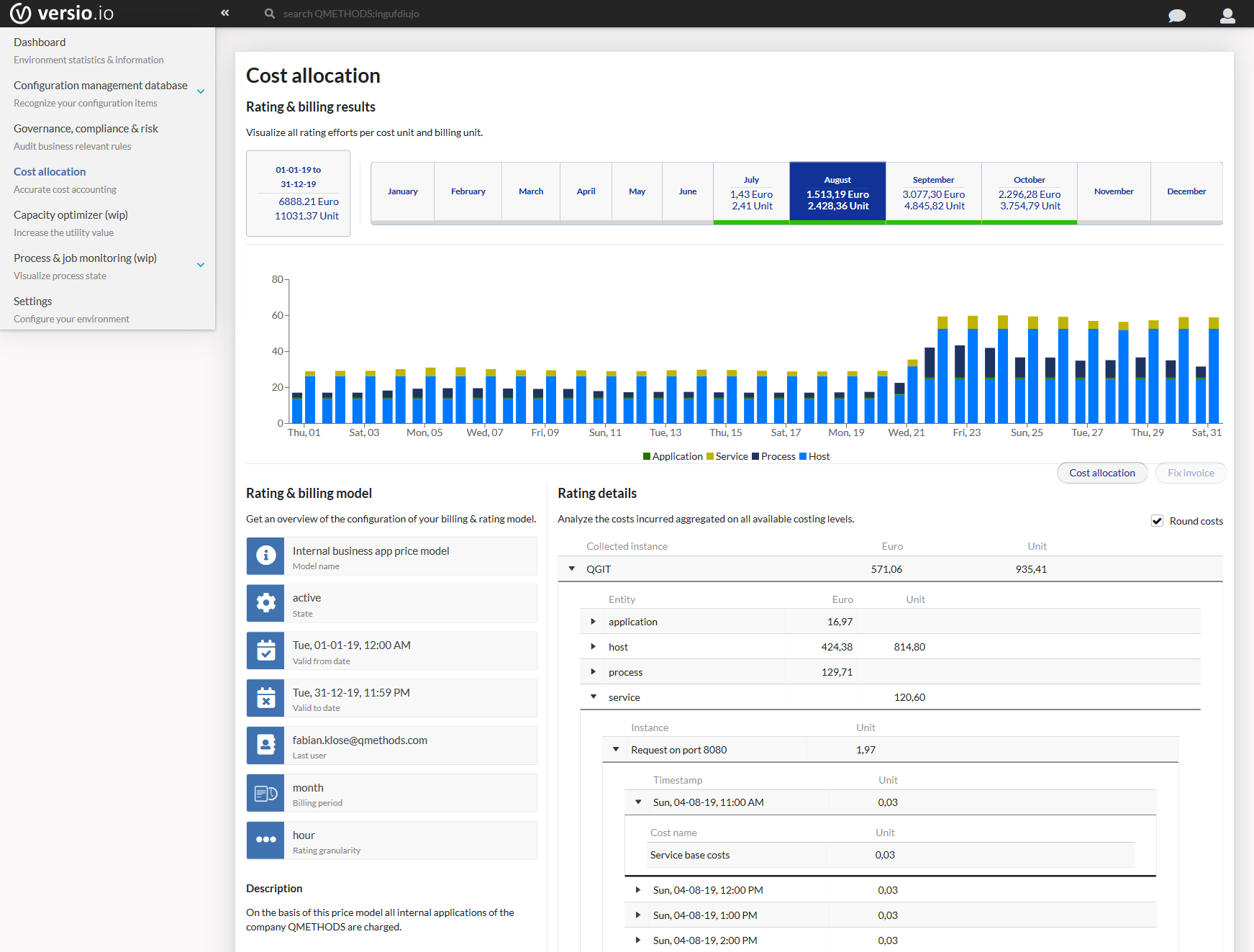
Service cost allocation
The service topology provides an excellent basis for the billing of costs or the provision of services.
Even dynamic resources that are only used temporarily can be taken into account due to the Versio.io topology and historization.
Define your customized pricing model for each component type and automate the continuous rating and billing of service costs.
The visualized accounting per period summarizes the incurred costs and allows you to quickly see how the costs have changed.
Read more

Asset & configuration inventory
Versio.io offers a central asset & configuration inventory with automated full-stack detection for your infrastructure, application and organisation landscape. This digital twin enables more efficient DevSecOps and IT operations.

IT governance
The Versio.io IT governance solution supports companies to formalise compliance with internal and regulatory requirements and automate their monitoring. All breaches are mapped in the risk matrix depending on the protection requirement assessment.
Contact us


Keywords

