Multiple win with a digital twin
Unlock potential with the digital replica of your IT landscape for DevSecOps, IT service management & IT operations management
In a nutshell Request demo Free trialWhat is a digital twin?
 A digital twin in IT enables companies to create a virtual represenat of existing
physical assets such as servers, networks, applications or other systems. This gives
companies a more efficient and secure control capability. Digital twins have been
used successfully in industry, manufacturing and healthcare for some time.
A digital twin in IT enables companies to create a virtual represenat of existing
physical assets such as servers, networks, applications or other systems. This gives
companies a more efficient and secure control capability. Digital twins have been
used successfully in industry, manufacturing and healthcare for some time.
X![]()
X![]()
X![]()
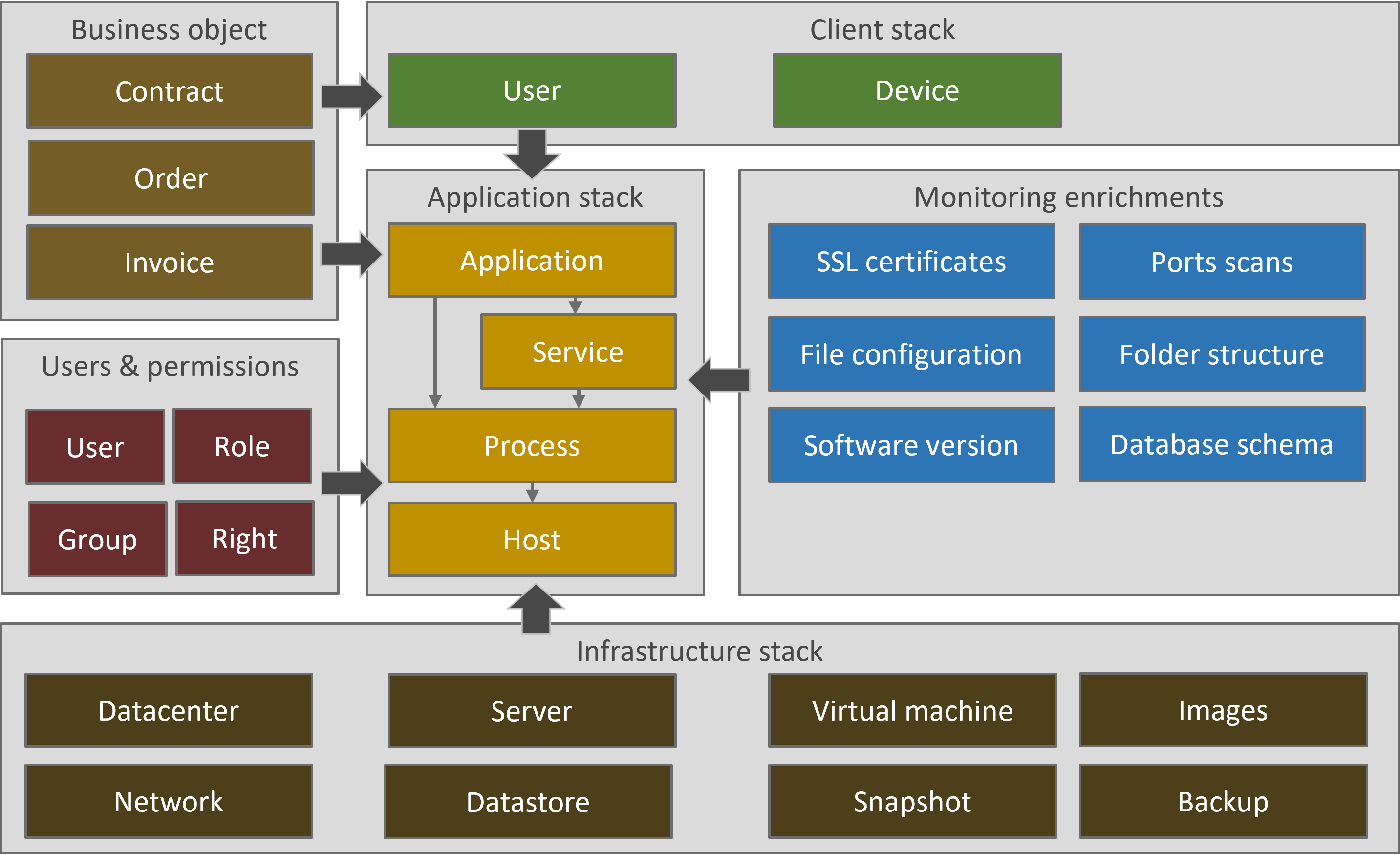
Use scenarios in IT
- Continuously updated IT documentation
- Recognition of changes
- Monitoring and evaluating the execution of change requests
- Verify regulatory and internal requirements for IT governance compliance
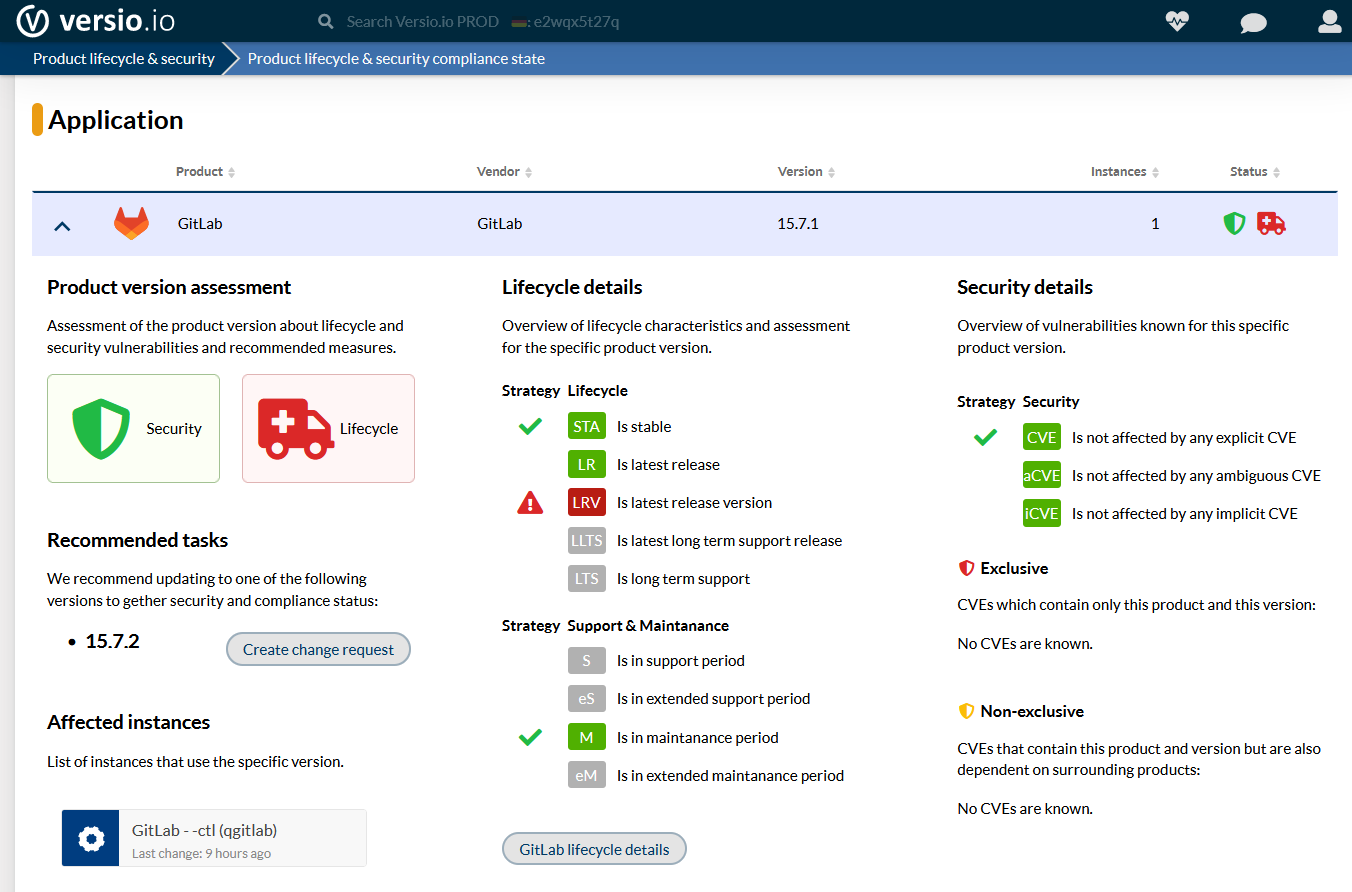
- Identify deployed and obsolete software versions (patch management) and security-related vulnerabilities (product and version-specific security vulnerabilities and configurations)
- Allocation of dynamically used IT resources
- Monitoring of specifications from Enterprise Architecture Management
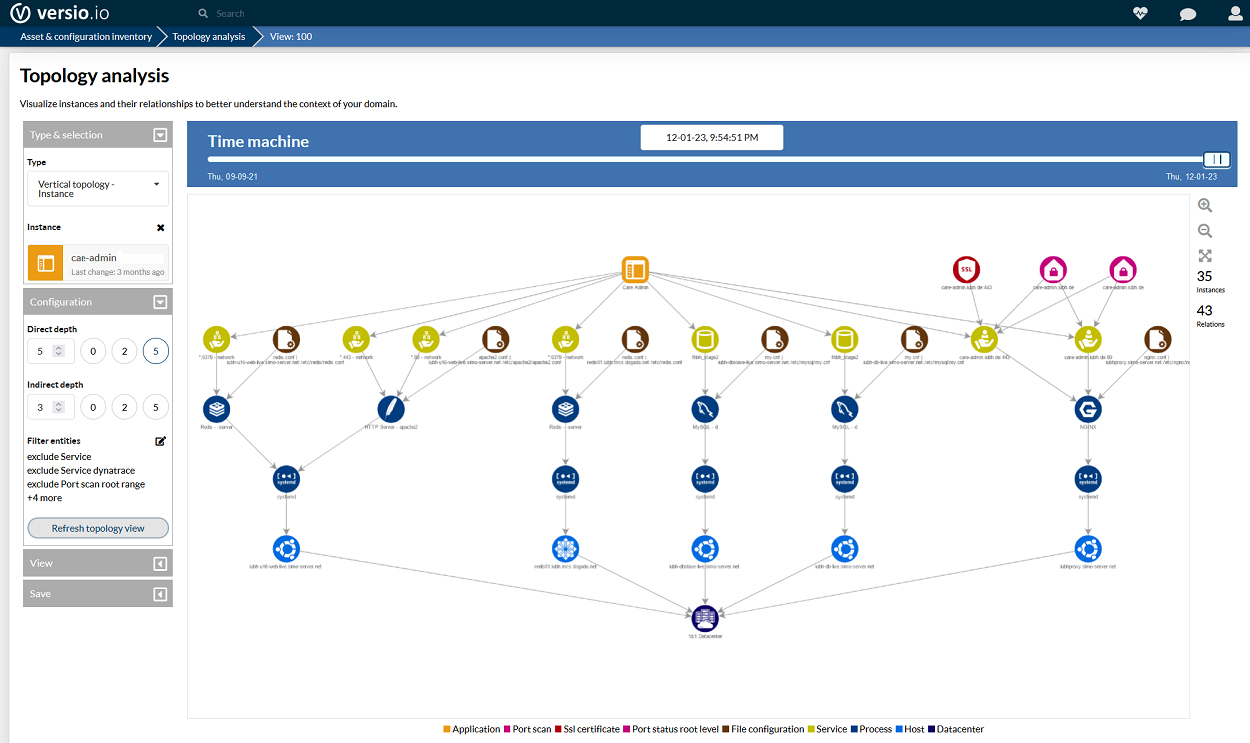
- Comparison of complex topologies (e.g. database schema between TEST and PROD environment)
- Process mining based on process changes
X![]()
Benefits of using a digital twin
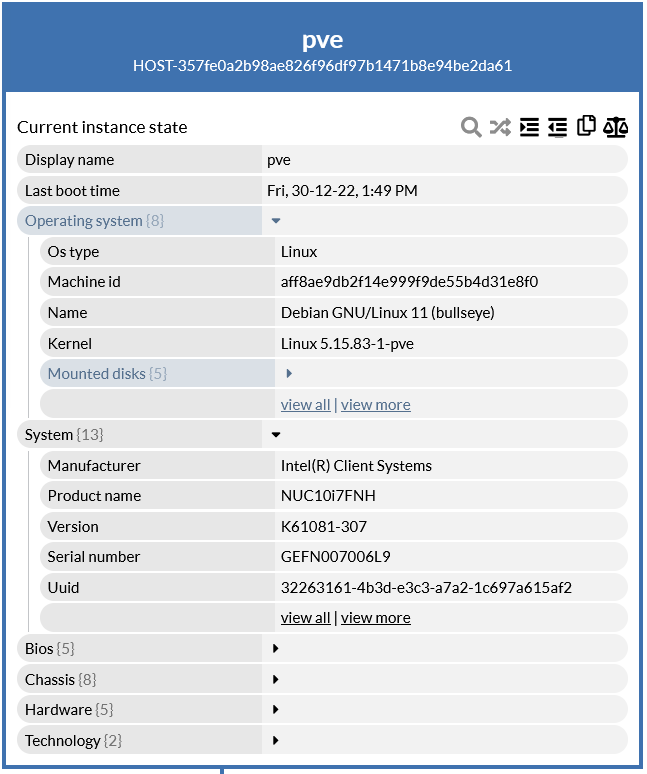
- Centralized and location-independent information provision across the entire IT landscape.
- Availability of information about the current status including the historization of changes to all IT components for problem analyses, audit security or recovery after a total failure.
- Mapping of the overall context of all captured IT components from the different data sources (Ex: connection between SSL/TLS certificate and related IT service).
- Increased security, as internal and external employees do not need direct access to the executed IT component, but only its digital image.
- Simple data provision or integration for third-party systems on the basis of the information held and consolidated in the digital twin. (e.g. DevSecOps, ITSM).
Author | Januar 2023

Keywords

